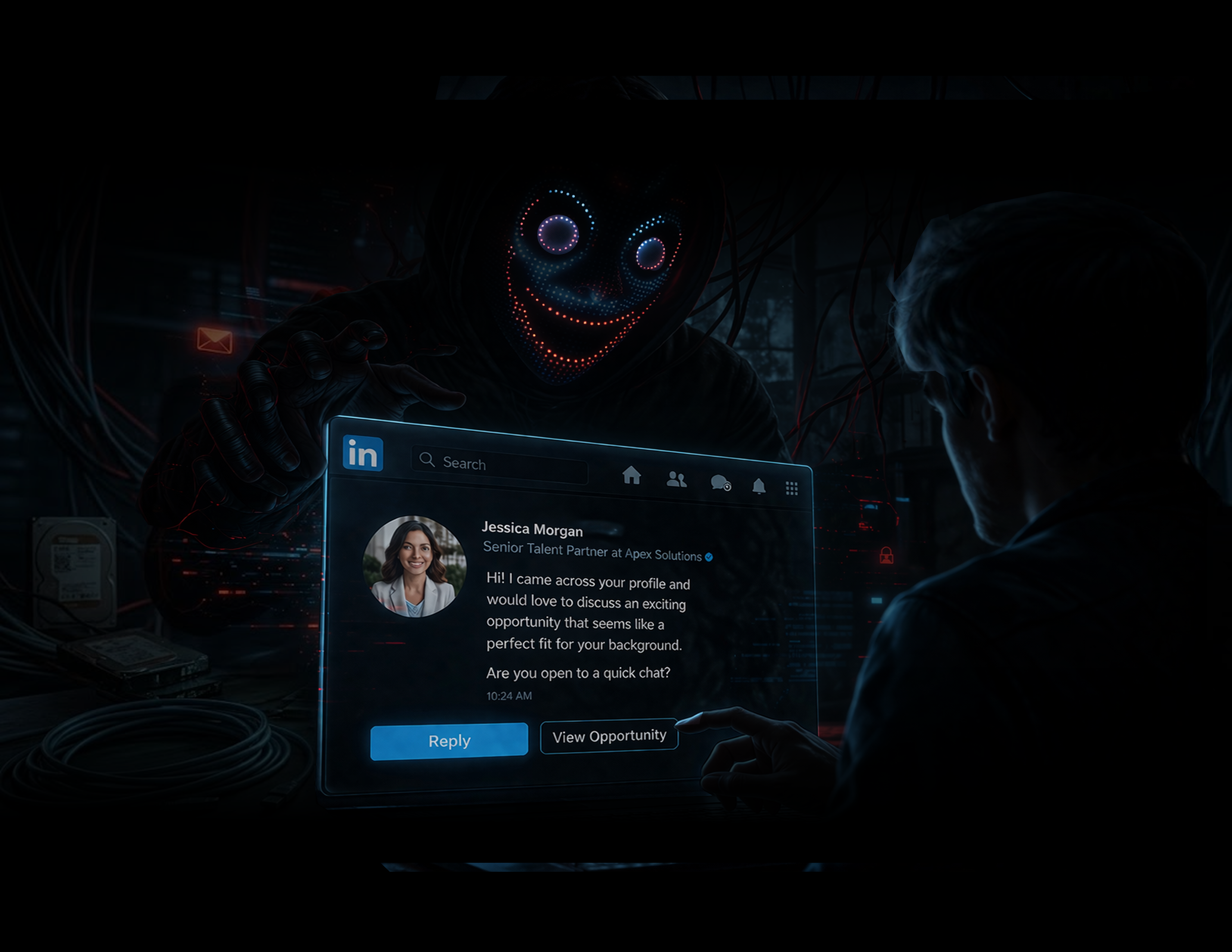
LinkedIn Recruitment Scams: The Social Engineering Threat Targeting Your Employees
A fake recruiter message is one of the most effective cyberattack methods today—because it doesn’t feel like an attack at all.
It feels like opportunity.
A new role.
A better salary.
A connection worth responding to.
As outlined in the original concept , this is exactly why LinkedIn recruitment scams are so dangerous—they blend seamlessly into normal professional behavior.
And that makes your employees the perfect target.
Why LinkedIn Has Become a Prime Target for Cybercriminals
LinkedIn is built on trust:
- Real names
- Real companies
- Professional conversations
But that same trust is what attackers exploit.
Scammers create:
- Polished recruiter profiles
- Convincing job offers
- Realistic company branding
The result?
👉 A cyberattack that looks like a normal business interaction.
The Real Danger: Social Engineering Over Technical Hacking
These scams don’t rely on sophisticated malware—at least not at first.
Instead, they rely on:
- Psychology
- Urgency
- Authority
The goal is simple:
👉 Get the user to take one small action.
That could be:
- Clicking a link
- Downloading a file
- Sharing personal information
- Moving the conversation off-platform
Once that happens, the attacker gains leverage.
How LinkedIn Recruitment Scams Actually Work
These attacks follow a predictable—and highly effective—pattern.
1: A Convincing Recruiter Reaches Out
The message looks legitimate:
- Professional tone
- Relevant job opportunity
- Recognizable company name
Nothing raises suspicion.
Step 2: The Conversation Moves Off LinkedIn
This is a critical turning point.
The attacker encourages communication via:
- WhatsApp or Telegram
- External “recruitment portals”
👉 Why? Because it removes LinkedIn’s built-in safeguards.
Step 3: A “Legitimate” Next Step
The victim is asked to:
- Download an “interview package”
- Complete an “assessment”
- Log into a portal
- Review onboarding documents
These actions often contain:
- Malware
- Credential harvesting pages
- Data collection mechanisms
Step 4: The Exploit
At this stage, attackers may:
- Steal login credentials
- Install malware
- Request sensitive company data
- Ask for payments or “fees”
And because the interaction feels legitimate…
👉 The victim often complies.
Step 5: Urgency and Pressure
If the user hesitates, the attacker escalates:
- “Limited opportunity”
- “Fast-track hiring”
- “Complete this today”
This pressure reduces critical thinking—making mistakes more likely.
Red Flags Your Employees Need to Recognize
Education is your first line of defense.
🚩 Red Flags in Job Offers
- Vague job descriptions
- Unrealistic salaries or benefits
- Minimal interview process
- Poor or inconsistent company presence
🚩 Red Flags in Recruiter Behavior
- Requests to move off LinkedIn quickly
- Use of personal email accounts (Gmail, etc.)
- Avoidance of verification questions
- Inconsistent communication
🚩 Immediate “Hard Stop” Warning Signs
- Requests for money or fees
- Requests for personal or financial information early
- Requests for verification codes
- Requests for internal company data
👉 These are not red flags—they are deal breakers.
Why These Scams Are So Effective
These attacks succeed because they:
- Blend into normal workflows
- Target employees directly
- Bypass traditional email security tools
- Exploit human behavior—not system vulnerabilities
👉 This makes them one of the hardest threats to stop with technology alone.
The Solution: Simple, Repeatable Security Habits
At AllSector Technology, we recommend focusing on behavioral security defaults:
1. Verify Before You Trust
- Confirm recruiter identity via company website
- Check LinkedIn profile history and activity
- Validate job postings independently
2. Keep Conversations On-Platform
- Avoid moving to external apps too early
- Use LinkedIn messaging until legitimacy is confirmed
3. Implement “Hard Stop” Policies
- No payments for job opportunities
- No sharing sensitive information early
- No downloading unknown files
4. Train Employees Regularly
- Conduct phishing and social engineering training
- Share real-world examples
- Encourage reporting without fear
5. Make Reporting Easy
- Provide a clear process for suspicious messages
- Respond quickly to potential threats
- Reinforce a “see something, say something” culture
Why Employee Awareness Is Your Strongest Defense
Technology alone can’t stop social engineering.
Your employees are:
👉 The first line of defense
👉 The most targeted attack surface
👉 The biggest opportunity for prevention
When they know what to look for, these scams lose their power.
How AllSector Technology Helps Protect Your Team
We help businesses reduce human risk through:
- Security awareness training programs
- Phishing simulation campaigns
- Endpoint and identity protection
- Incident response planning
We turn your team from a vulnerability into a security asset.
Final Thoughts: Not Every Threat Looks Like a Threat
The most dangerous cyberattacks don’t look malicious.
They look like opportunity.
They look like growth.
They look like normal business.
👉 And that’s why they work.
Want to protect your team from social engineering attacks?
Contact AllSector Technology today for a Security Awareness Assessment and strengthen your human firewall.